At present, there are configuration options about NPT in vyos version, but they seem to have no effect. Does anyone know how to implement this feature.
Referring to H3C, NPT is also called nat66 technology. In fact, it is SNAT and DNAT implemented by IPv6. Different from IPv4, nat66 only supports 1-to-1 mapping of routing prefix, which will provide vyos with nat66 experimental support supporting SNPT and DNPT. This implementation needs to be tested. Please summarize all bugs and modification suggestions under this task for tracking.
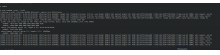
set nat66 source rule <ruleid> description <description> set nat66 source rule <ruleid> disable set nat66 source rule <ruleid> log set nat66 destination rule <ruleid> oinbound-interface <interface> set nat66 source rule <ruleid> source prefix <prefix> set nat66 source rule <ruleid> translation address <prefix>
set nat66 destination rule <ruleid> description <description> set nat66 destination rule <ruleid> disable set nat66 destination rule <ruleid> log set nat66 destination rule <ruleid> outbound-interface <interface>|any set nat66 destination rule <ruleid> destination address <ipv6-address>|<ipv6-network> set nat66 destination rule <ruleid> translation address <ipv6-address>|<ipv6-network>
I refer to the configuration structure of H3C. In the original command structure, NPT does not support the division of SNAT and DNAT. In order to implement nat66, I separated it for the following reasons:
- I can modify it according to the existing script of NAT, and I can modify it less nat.py , I created nat66 and the independent nftables-nat66.tmpl to complete the implementation of nat66.
- It can fully support the configuration of SNPT and DNPT in nat66. If users do not need SNPT or DNPT, it should not take effect by default.
My initial implementation of npt is in:
Since the current branch uses the kernel Linux 5.10, I began to pay attention to the implementation of NPT again. At present, I have completed the following features:
- SNPT 1:1 mapping
- SNPT Address Mapping
- DNPT single address mapping
- DNPT 1:1 mapping